Backups Are Essential
Like many people - though not enough people in my opinion - I like to keep all of my data backed up. Pictures and videos we've taken over the years, important documents, notes, music I've written, network configuration files, that old Minecraft map I spent 100's of hours building in 2016 and never touched again... All of the important things that make up my digital life.
Given the huge portion of our actual lives that already is, or is rapidly going digital, losing that information would be a huge loss. For that reason, backups are essential to me.
In this article I'm going to take you on a journey through the difficult way that I've chosen to handle my backups, and why I do it the way that I do.
But first, a little background...
Backups AREN'T Hard
"But wait... the title says..." - Yes, I know, dear reader, but really I meant backups are hard for me. For most people, they are not. The Tech industry makes sure that it isn't difficult at all for many people to at a minimum back up their photos, videos, and app data. On Android you have Google Photos, Google Drive, and other Google cloud products for your memories and documents, as well as your phone manufacturer's cloud backup service for app backups. Apple has iCloud, of course, which fulfils all of these roles for iOS, iPadOS, and Mac users, and you have Windows Backup (OneDrive), which is Microsoft's cloud offering for your PC. There are also common 3rd party solutions you can choose to use instead, like Dropbox.
All of these services, plus many others, provide free backups up to a point, and storage is cheap and generous if you need a paid tier.
OK, so what's the problem? Well, free and cheap aren't really free and cheap. You're still paying something. With these services, your data is not private. These providers (not you) actually hold the encryption keys that are used to encrypt your data on your device before sending it up to the cloud. That means they can decrypt it any time they want, and many state in their privacy policies that they may use your personal files to improve their services, for advertising purposes, or to share with "affiliates and trusted 3rd parties" - and this means that company employees also have access in limited cases.
In addition, these services are proprietary and closed source, which means you can never verify whether they are actually protecting your data in the ways that they say. Has anyone at these companies actually gone combing through your photos? Probably not, but the point is you can never know for sure.
Many other companies, for example Proton Drive, NordLocker, Sync.com, Mega.nz, and many others promise you that your data is fully encrypted End to End, and ONLY YOU have access to it. These cost more, many providing up to 2 TB for about $10 a month, but they can be a much better solution than relying on your built-in Google, Apple, Samsung, etc. solutions with dubious or non-existent privacy.
Again, though, much of their code is proprietary, so nobody but them can know if your data really is safe and secure!
Personally, I don't want even the slightest chance that someone else can view my pictures or read my notes - that stuff is private after all - or at least it should be.
To summarize, default cloud services built into your device are super easy, usually free and sometimes even enabled by default (beware!), but they provide little or no privacy. Encrypted cloud services cost a little more, but provide much better promises of privacy and security.
Types of Backups
There are 3 main types of backups you can make, Local, Offsite, and Cloud (technically Cloud is also offsite, but I've left it separate because there are other types of Offsite backups other than just Cloud)
- Local Backups: This is easy to do, and hard drives are pretty cheap these days. This is not a very good method of backup, however, as a natural disaster, flood, or fire can ruin both your main copy, AND your backup! In addition, modern SSD drives don't last forever and can begin to lose data after just 4 years! Additionally, reliability can vary widely between brands.
- Offsite: The next best thing, you can make a copy on an encrypted drive and give it to a friend or family member for safe keeping. Definitely better, but if you live close, a natural disaster could still wipe out both copies. Additionally, just like local backups, you can lose data if you get a bad SSD or flash drive, and data can fade over time. You may not know whether you still have your data until you lose something and need to restore it!
- Cloud: The best solution for data longevity, as modern data centers have much higher reliability, but this is also a more expensive solution or, as discussed earlier, can open you up to privacy and security issues depending on who does the storing.
Sometimes Backups ARE Hard
So really, you kind of have to think through a lot, and maybe work a bit to find a good solution that works for you and your particular needs. If you want secure, private, reliable storage for your precious data, it takes some homework.
So all that being said, I'd like to take you on a tour of my backup solution. This is probably overkill for you, as multiple Offsite backups could be your best bet, but being a nerd, I like to find even better ways, even if they are not that easy to set up.
I'll break this up into categories by device, since that is the way that most people think about their backups.
- Browser Links (Tool: xBrowserSync) This is a small one, but it makes a big difference. Since we sort of live in our browsers these days, having links synchronized privately and encrypted between your various browsers and devices devices is a must. Here again, though, built-in solutions may or may not be truly private (in Chrome they definitely are not since, here again, Google has access to your credentials), and if you have different browsers that you use, you can't share your links easily between them. xBrowserSync is both cross-platform (plug-ins for Chrome, firefox, as well as mobile apps) and open source, so it can be audited by anyone to make sure it is really doing what it says it is.
- Phone and iPad (Tool: Syncthing) Syncthing is a great open source automated backup tool that runs in the background and makes copies of your data between devices. This isn't necessarily a cloud solution per-se, but it does make it easy to bring all your device data together in one spot (and if you're so inclined, you can cheaply host your own Virtual Private Server in the cloud that can run Syncthing!) I have a Syncthing app on my phone, my iPad (Mobius Sync), and my laptop. I have android apps that I care about export their backups (either automatically or manually) into a specific folder on my phone, and these get instantly backed up to my laptop, within seconds of any new files being added! I also have my password manager database backed up with Syncthing to all of my devices. Again, Syncthing is open source, so the risk that they've got something to hide is much lower.
- Laptop (Tool: Duplicity and Mega.nz) Duplicity is another great open source tool that can encrypt and store your files. It will automatically compress your files using a passphrase of your choice, and split the compressed archive into 200 MB chunks that can easily and privately be stored anywhere you want. Since Duplicity fully encrypts my files, I didn't feel icky about using a cloud service to store my archives. There are many great choices for this, such as Proton, Sync.com, NordLocker, Mega.nz, and many others. I personally chose Mega.nz because they are relatively cheap, have no 3rd party trackers or advertising on their website, and promise full end-to-end encryption - again, not 100% trustworthy as much of their infrastructure code is closed source, but since I am encrypting my files myself first, I am OK with this. Duplicity is a terminal application (command line), so some basic knowledge of the command line is necessary. Note that I do also have an additional local backup of my files, for easy retrieval should I need them, but less safe than my cloud solution.
This is a lot! Here is how my data flows, fully encrypted "in transit" along the whole path, as well as encrypted "at rest" in a local drive and on Mega.nz:
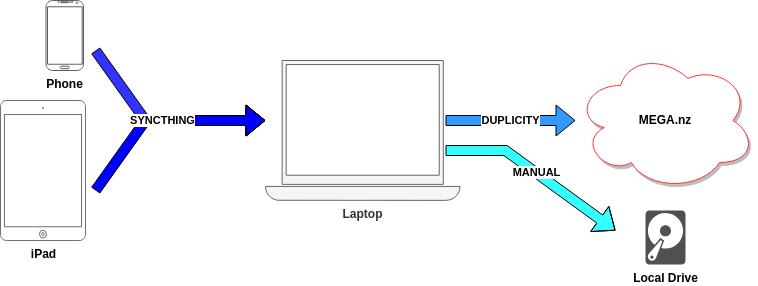
It seems simple in theory, but it takes a LOT of setup to get it just right. While Syncthing is relatively well documented, the documentation for Duplicity is very technical, and it took some real fiddling to get it to work the way I wanted.
Just to illustrate, after hours of tinkering, here is the final command I use in order to connect to Mega.nz and upload my backups, tweaked slightly so I don't give away too much. (Secret-tool is a linux-based password manager that can be used at the command line, and enclosing it in `` runs that command first, and replaces it with the output password so that you don't have to hard-code it and make it vulnerable):
PASSPHRASE=`secret-tool lookup duplicity pass duplicity full -v 5 --progress /home/me/backups megav2://email@example.org:`secret-tool lookup mega pass`@mega.co.nz/backups
Technical Stuff: The PASSPHRASE variable is the encryption key that is used by duplicity to encrypt all of my files. Then I have the option "-v 5", which is verbosity level 5, so I can see all of the filenames as it is placing them into each archive chunk. The "--progress" option gives me a % complete readout every 3 seconds, then there is the source folder "/home/me/backups" and finally the call to the Mega.nz API in order to communicate directly with their servers and transfer the completed chunks straight from duplicity into the "backups" folder in my cloud drive.
Summary
So, as you can see, my setup isn't super easy... In fact, it's pretty hard! But I am confident that it is private, secure, and reliable. Plus, watching all those filenames scroll by in a terminal window with Duplicity running is really fun :).
Anyway, all of this is a long-winded way for me to say - think really hard about how you back up your data, and whether privacy and security is important to you. If it is, it's not easy, but there are solutions for every kind of person!