Update 4/13/22: Added additional source references and tool recommendations.
Why worry about privacy? ("I've done nothing illegal…" or “I'm not afraid of Google...”)
While we expect to some degree to have to hand over information to organizations like our employer and our bank, and for services we enjoy such as media streaming services, we don't always know where that information goes once it gets there, or even exactly what information they're taking. It's almost always more than we normally think about. That's why it's important that we work hard to give up as little of it as possible.
It's OK to hand over information for something legitimately valuable to you, but you must be diligent and make sure that it is worth it for what you are giving up.
Even if you don't fear your data being under the control of any particular company, remember this: companies and governments are merely entities made up of individual people. Individual people can be tempted, corrupted, or fooled through social engineering. They can also precipitate unintended consequences from otherwise well-intended policies.
Remember too, that technology - especially machine learning - is advancing rapidly, and your data might be used for purposes in the future that it can't be today. More and more, these sophisticated algorithms are working towards predicting our thoughts and actions. Even more than your physical body, your thoughts are who you are. Your mind is where you live, and if these algorithms are fed enough information about your past actions online and in the physical world, your individuality as a human being, and your very identity, might be at risk.
How bad is it, really?
Data brokers combine data from many different online sources with real-world information about us, and then sell this data to whomever is willing to pay for it. These entities can be far worse than well-known companies like Facebook and Google. It's impossible to be online without an ISP, yet they too have a record of selling your location history.
This information can be used against us just as easily as it can be used to provide us with services, giving us recommendations on movies, or targeting us with personalized advertising.
Furthermore, our data comes from more places than you may know. Here are just a few examples of sneaky (and a little creepy) ways to get information about us, just to illustrate the point:
- Whenever you share your contacts list with an app or website, all of that information about your friends and family is given away without their consent, and can't be clawed back.
- Unnecessary apps and add-ons like GIPHY or Emoji keyboards collect our IP address and other user data in exchange for relatively little gain.
- Third-party keyboard apps like SwiftKey and GBoard log everything you type and share it with companies or people you don't know.
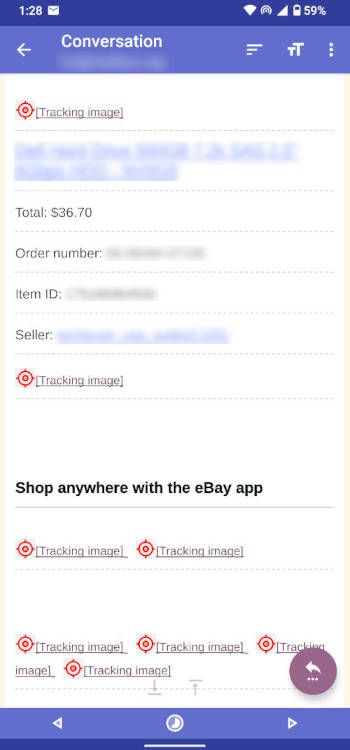
- Images, even all-but-invisible ones called spy pixels, are included in many emails that tell senders your IP address and when you opened the email, without even asking you for a read receipt. This can be misused for unintended purposes.
- Your grocery store uses your loyalty program and location tracking to obtain information about what you buy, and then sells that information to 3rd Parties, who can market to you in sometimes creepy ways.
We willingly give away our data by using these services, whether we like it or not.
Your IP address and other identifiers transmitted to these services can be used to determine your approximate location, and even "anonymized" or "de-identified", they can still identify who you are. It becomes increasingly important to know what you share with whom, and how far you can trust them.
Let's continue with the example of GIPHY. Now that they are owned by Meta/Facebook, there are some concerns about their sharing of information with that platform. Did you know they reserve the right to collect data from you even if you are the recipient a GIF someone else sent you?
Here is an excerpt from GIPHY's privacy policy:
...We automatically receive and record information from your web browser or device when you interact with the Services, including when you search for, select, view or receive a GIF, such as your IP address, device ID, user query information and cookie information...
Why should I care?
Here are some reasons why you really should take your privacy seriously:
- First, it’s about preserving your rights. Privacy is a fundamental human right (according the American Library Association's interpretation of the UN's 1948 Universal Declaration of Human Rights) - and we’re giving up that right piece by piece for the sake of convenience and cutesy little add-ons like GIFs… We skip over Privacy Policies because we are too lazy to read them, and blindly agree to all the terms.
- We need privacy in order to be safer from hackers, stalkers, identity theft, blackmail, and foreign governments (even your own government, too). Hackers can do surprising amounts of harm with surprisingly small amounts of data. Data breaches and leaks happen more often than you hear about.
- Too many companies know our exact location at any given time, our daily habits, our demographics, our schedules, who we‘re with, what we do there, and why. With sophisticated AI, they can predict our moves, our personality, our values, and our wants and needs. Even our sexual desires, fetishes and activity with partners are bought and sold using our browsing history, ISP traffic, and physical location. Brick and mortar stores are also beginning to track your location within the store using techniques like facial recognition and scanning of our WiFi and Bluetooth devices. These techniques are even being employed in airports and museums, as well as workplaces to track employees.
- Regular carrier SMS messages are not encrypted, and are never private. Large email providers like Google and Yahoo save your entire email - text, pictures, and attachments - for later analysis and future advertising opportunities. This includes medical info - HIPAA protections do not extend to your email provider, although there is some legislation beginning to be proposed for this.
- Most tech companies and data brokers factor in data breach lawsuits and insurance as a cost of doing business, many times in place of governmental oversight and regulation. This allows them to consider the security and privacy of their customer data through the lens of cost/benefit analysis. If the cost to implement better security and data governance policies is greater than the threat of financial harm of a data breach or the cost of insurance, they may not always opt for the former, even though insurance underwriters encourage sound cyber security policy.
- Many companies are not always concerned about harm to individuals unless there is a threat of major reputational harm, and even then, having a product in high demand can help them ride it out, or undergoing a rebranding can change the conversation.
- Governments are turning more and more toward the same AI/deep learning algorithms as advertisers, but using it for much more worrisome purposes with serious implications, currently with a bias against minorities.
OK, great, but... it is what it is, right? What can I do about it anyway?
-
Compartmentalize to limit any one entity's knowledge of your life.
Examples include:- Complete separation of online vs. offline identities (i.e. don't use your real name, age, location, or other attributes. Make them up if you can.
- Never ever ever ever reuse passwords or use similar passwords. Use a good password manager (recommendations below) to generate 24-character or longer random strings to use as a password.
- Use separate accounts for public, personal, and work-related tools or services.
- Use different services for Email, chat, calendars, document production, cloud storage, etc., etc. (I have some recommendations for each of these later on). Don't put all your data eggs in one basket no matter how convenient (Google).
- Only use services that are conscious about your privacy. Not all of these services are free, but if you are not willing to put a price on your own privacy, others absolutely will, and already have.
- Always use different usernames for each company or account (a password manager can help with this).
- Limit reuse of email addresses between companies where possible.
-
Secure and protect your information,
including but not limited to:- Using end-to-end encrypted communications only, when at all possible. Your data should always be encrypted, both in transit and "at rest" (where it is stored).
- At the very least, set up an alternative private email service like Tutanota or ProtonMail for highly-sensitive data, and use chat services such as Threema or Signal.
- Pre-vet any and all apps you download using a service like Exodus Privacy.
- Use a de-googled Android phone like a Pixel running GrapheneOS or CalyxOS. iPhone is not a good alternative to this. Don't use a Samsung or Xiaomi phone.
-
Stay anonymous where possible.
Examples include:- Use different browsers for different devices and types of activity. Use add-ons like uBlock Origin or Privacy Badger in your browser to block some advertisers and trackers.
- Browser: Use a more privacy-conscious one (recommendations below), but disable javascript at a minimum. This breaks nearly all websites, but you can selectively enable each domain (NoScript add-on) and selectively enable those you are willing to trust, or even see the names of individual scripts (Brave browser).
- Use a trusted VPN or TOR (not both at the same) on select devices to encrypt your traffic and hide the websites you visit from your ISP.
- Again, don't use real facts about yourself such as age, location, attended schools, likes, pet names, car make or model, etc. Never use specifics. When you have to use specifics, like in security questions make them up and store them on paper.
And for cripes sakes, if you don't HAVE to put it online, DON'T!
-
Avoid using Internet of Things (IoT) devices.
Security is not always their priority, especially in budget devices. The more devices you have on your network, the more potential points of entry there are. -
Inform yourself!
- Always fully research any company before doing business with it. Look for bad reviews, previous data breaches, everything you can dig up.
- Read Terms of Service and Privacy policies. They are incredibly revealing. It can be a head-splitting read, but you soon adapt. If you don't understand it or feel uncomfortable, don't do business with them. Find an alternative - there almost always is one.
- Ask companies to show you what data they have on you. More and more companies are allowing you to request your data, with services like Google's Takeout and Amazon's Request My Data. It isn't always easy to read, unfortunately. You can even try to ask them to delete it.
- Keep up with data breach news - don't trust any company to notify you of a breach. They almost never will, unless they absolutely have to.
- Regularly check HaveIBeenPwned for compromised email addresses, phone #s, and passwords.
-
Act and support!
- Support your favorite open-source software! The people who created them deserve it, for they work hard to keep it safe and up to date. Firefox is dying! Don't let chromium-based browsers be the only choice!
- Educate family and friends. The more people that understand this and can make an informed decision, the greater pressure lawmakers will feel to do something to limit entities' broad reach and misuse of individuals' data.
-
Don't panic.
You can't fix this all right now. It will take time, and it won't ever be 100% perfect… just do what you can. Chances are, it won't take you as long as you thought to adjust, and some solutions you will find to be better than the big guy's product anyway.
An important word about VPNs
Many people recommend using a VPN as a one-stop foolproof way to protect your privacy. This is false. A VPN merely shifts the burden of trust from your ISP to your VPN provider. Right now, this is mostly for the best, as ISPs have a terrible track record with providing you with any sort of privacy. It can also be dangerous to believe what people say about VPNs, because many people get a VPN, think they're safe, and otherwise let their gurard down.
What a VPN cannot do:
- Stop websites from tracking you. This is mainly accomplished through cookies and javascript inside your browser.
- Make you anonymous. True anonimity is very very difficult to achieve, and involves serious forethought, study, and commitment. Think cash for everything, endless burner phones, fake identities - real tinfoil hat type stuff. Which is great, if you are willing to put in the effort (most aren't).
What a VPN can do:
- Hide your traffic from your ISP. While your actual activity is hidden by encryption provided by HTTPS, the destination of your traffic is not. Basically it is exactly the same as your browser history.
- Protect your mobile traffic from public or guest WiFi. Always use a VPN when you are on someone else's network. Even when visiting family.
A VPN is part of a balanced privacy diet for sure, but stay aware of news about your provider and changes to your provider's privacy policy. Also, it's best not to put all of your traffic - phones, PC, iPad, IoT, etc. - through one and only one channel. Don't let any one entity know everything you do.
Privacy vs security vs anonymity
There is a complicated relationship between these 3 things, and they are not synonymous, nor are they mutually exclusive:
- Privacy is impossible without proper security.
- Your data on its own, or with any company is only as secure as the weakest link in your or their network (and workforce).
- Privacy does not always require anonymity, but it is necessary in some cases, especially when data brokers combine datasets about you across multiple services and sources.
- Anonymity does not guarantee privacy.
- Even "Anonymized" statistics can still tell a lot about you, and be used to identify you.
A Short List of recommended tools/services
- Browsers
- Desktop: "Hardened” Firefox (see below - safest choice), TOR Browser, or Brave (quick/easy setup)
- Even if you use chrome (but don't), at least disable javascript.
- iPad/iOS: Brave or Onion Browser
- Android: "Hardened" Firefox/Fennec, Bromine, or Brave
- Private DNS (encrypted DNS queries, may provide global ad/tracker/malware domain blocking depending on the provider)
- Quad9
- dns.adguard.com - blocks not only ads, but some sites that host trackers and malware. This can also be set up globally on Android with the "Use secure DNS" network setting. Only one word of caution - be vigilent, as AdGuard started as a Russian company, although they moved their headquarters to Cyprus in 2014.
- Extra credit: “Roll your own” with Pi-Hole!
- Note: when using these solutions , you'll need to disable your browser's built-in “DNS over HTTPS” setting. These usually automatically connect to Cloudflare or another provider. Bad.
- For more about DNS, see my post on it here.
- Backup
- Syncthing (from a mobile device to a PC or between PC's using SyncTrayzor)
- ownCloud
- NextCloud
- Sync.com (PC, Mac, iOS, Android) - easy setup, but still a company... encrypt everything before you store it.
- Password Managers
- Bitwarden
- KeepassXC
- Email
- Tutanota
- ProtonMail
- Mailbox.org
- FairEmail (Android mail client)
- Messaging
- Threema (anonymous)
- Signal (requires phone#)
- Session (anonymous)
- Maps and navigation:
- Organic Maps
- Osmand+
- Notes
- Trilium (self-hosted on a PC or cloud server)
- Mood Patterns (daily mood journal)
- Document Suite (Spreadsheets, Word processing, etc.): Cryptpad
- Search
- Searx (searx.org, search.disroot.org or other public instances)
- Startpage
- Swisscows
- Unfortunately, Duckduckgo can no longer be trusted (In fact, I was a bit leery from the start given who it's founder is).
- VPN:
- NordVPN
- Surfshark
- Private Internet Access
- NOT ExpressVPN
- Extra Credit: “Roll your own” using OpenVPN and a cloud server like Linode
- News:
- NewsBlur (better than most though not 100% perfect)
- Open source RSS readers like Tiny Tiny RSS
- Android app tracker scanning:
- Exodus
- Tracker Control (TC Slim) - also can block certain domains
- Watching Youtube Videos:
- NewPipe
- Alternatives to YouTube such as Odysee
- Settings and add-ons for “Hardening” Firefox: - Note, many of these settings, especially Noscript and the Arkenfox mod WILL BREAK SITES. I promise you will eventually get used to manually disabling select protections for sites that you trust.
- https://github.com/arkenfox/user.js/
- Add-ons:
- Noscript (most important)
- uBlock Origin (important)
- CanvasBlocker (optional)
- Chameleon (optional)
- Smart Referrer (optional)
- Skip Redirect (optional)
Great resources for further reading
- Wikipedia: Right to privacy
- Wikipedia: Psychographics
- Wikipedia: Self-sovereign identity
- Wikipedia: Internet Privacy
- Privacy International
- Restore Privacy
- HaveIBeenPwned.com
- “The Art of Invisibility” by Kevin Mitnick
- What info is my browser sending to websites?
- IP/DNS info leak detection
- Privacy Report: What Android Does in the Background
- Transparency Matters Blog
- 2021 Data Breaches (also check other years)
- Henry's Privacy Resources
- The Data Map
Well, that's my spiel. I hope you're still with me and that you're able to take some something positive away. I'm not trying to scare you, but give you a starting point, and some tools to help take your privacy back.
Here's to hoping you have a safe and secure future, that belongs to YOU.